Local
Locks and unlocks files on your machine.
Open source. Local and offline. Windows, macOS, Linux.
How it works
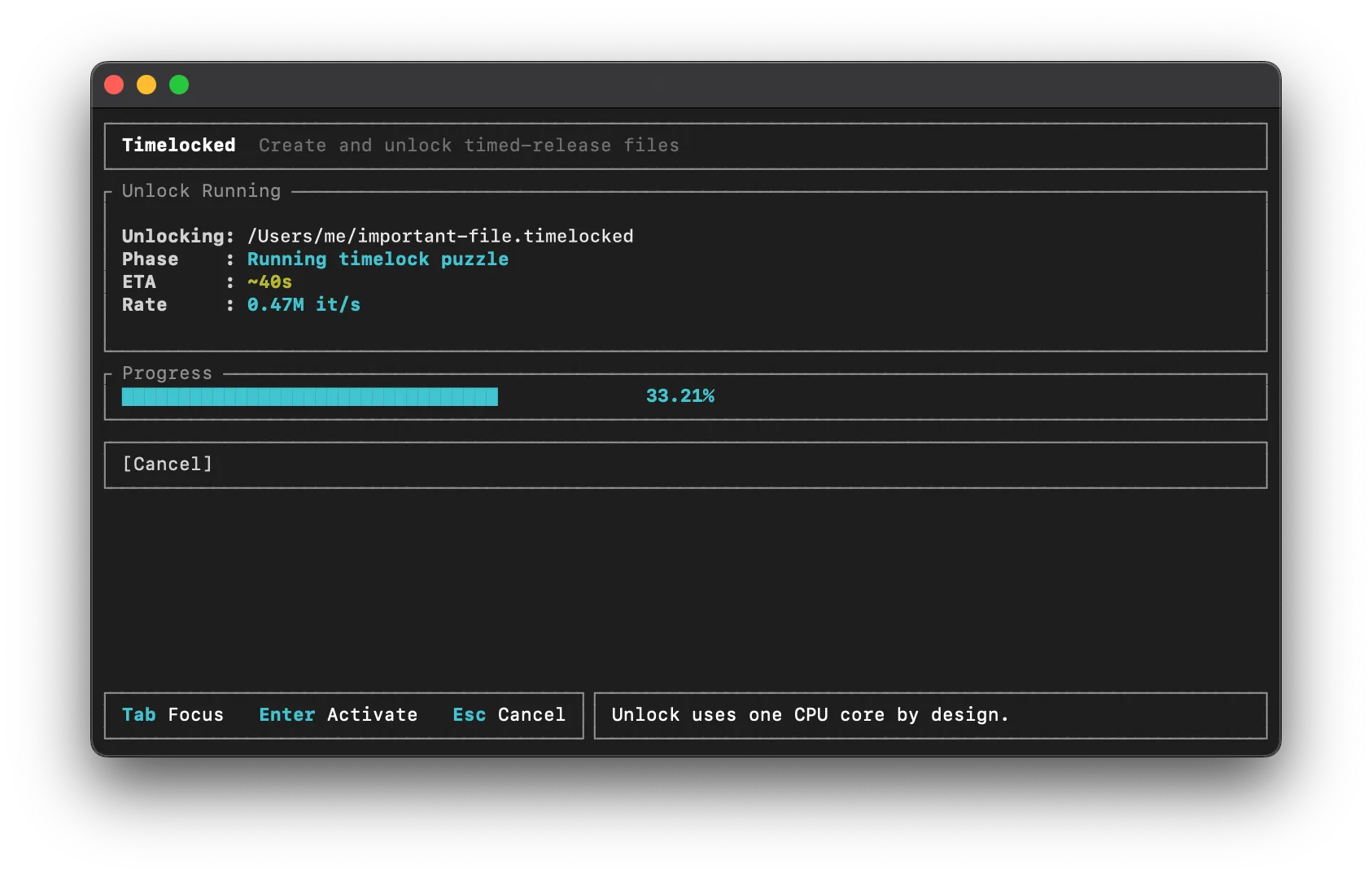
The file is encrypted with a key. The key is locked in a RSW style time-lock puzzle. Both the encrypted file and time-locked key are put in a binary .timelocked file. Unlocking only needs local, sequential compute work. Only one CPU core can be used to unlock, so parallelization wont help going faster.
Locks and unlocks files on your machine.
No internet use and no telemetry.
Portable builds for Windows, macOS, and Linux.
Around 3 MB with minimal dependencies.
Open source with CLI and TUI workflows.
Integrity checks, recovery support, and compatibility for older locked files.
Stop and continue long unlocks without starting over.
Cap CPU usage to preserve battery.
Use cases
Delay access to your own funds (or most of them).
Timelock a non-memorable BIP-39 passphrase and use temporary passphrase setup on your hardware wallet. Now, you need to wait hours/days before being able to sign any transaction. In duress situations, explain this to attackers who come to your house.
There’s no need to lie or omit anything; it’s easier to tell the truth under pressure. You can prove it to them by showing them your entire setup (including this site). Hopefully, they’ll realize that the risk/reward ratio is no longer in their favor.
Give family a recoverable path while keeping time to react if storage is opened early.
Time-lock documents and passwords with a long delay, for example 10 days. Store them on a USB stick with the Timelocked app and clear instructions.
Put the stick in a tamper-evident bag inside a safe. If the bag is opened early, you have time to rotate passwords before the delay completes.
When a file should exist now but open later.
Possible uses include fallback releases, such as investigations or scientific work, in case something happens to you. Other uses include journalism sources, legal or professional handoffs, puzzles and enigmas, delayed gifts, or delayed Rickrolling…
FAQ
Timelocked is not a cloud service. It is a local application. It does not require an account, does not connect to the internet, and includes no telemetry.
No. Timelocked enforces “do this much work” rather than “unlock at this exact date and time”. The actual duration depends on the machine that unlocks it and its current conditions, such as power mode, thermal throttling, and background load.
Because CPU clock speeds have improved slowly since the early 2000s, the delay should not usually shrink dramatically on a modern desktop. Still, calibrate conservatively if timing matters.
Timelocked turns a file or message into a locked package (a file ending in .timelocked). Anyone can copy and keep that package, but opening it requires making a computer do a long, step-by-step calculation. Because each step depends on the previous one, there is no practical way to “skip ahead” and open it early.
Technically, the lock phase generates a random symmetric key K, encrypts the original file/message with AEAD using XChaCha20-Poly1305, and stores the ciphertext in the timelocked file payload. K is then time-locked using an RSW-style repeated-squaring time-lock puzzle parameterized by T iterations. unlock performs the sequential work to recover K, then decrypts the payload back to the exact original bytes. Reed-Solomon error correction is added to protect against some file corruption.
Faster computers with higher CPU frequencies can do the required work faster, so the “delay” can be shorter on very powerful hardware. However, CPU clock speeds have improved slowly since the early 2000s. If your use case is important, choose a conservative delay and add a safety margin.
Quantum computers are especially relevant to some problems, including factoring. If large, practical quantum computers become available, they may be able to recover the secret factors used by the time-lock puzzle and unlock files much faster.
The goal is for the only realistic way to open a .timelocked file early to be doing the same long computation required by normal unlocking. There is not supposed to be a clever trick that jumps to the end.
Timelocked is designed so there is no known practical shortcut to recover the cryptographic key K faster than the required sequential work, for the chosen parameters and assumptions. It is based on Rivest, Shamir, and Wagner’s 1996 paper Time-lock puzzles and timed-release crypto.
Important nuance:
.timelocked file.The creator already has the original content at creation time. If they keep a copy, or share the key some other way, they can read it immediately.
Timelocked is meant to delay access for someone who only has the .timelocked file, including the creator if they delete the original content and do not keep the key.
Timelocked is not a backup service. If you lose both the original file/message and the .timelocked file, the content is gone.
If you lose the original but still have the .timelocked file, you can unlock later and recover the original.
If you lose the .timelocked file but still have the original, you still have your content; you just do not have the timelocked copy anymore.
If it matters, keep multiple backups of the .timelocked file and the Timelocked portable apps.
Sometimes, yes.
Timelocked v1 stores the encrypted payload with Reed-Solomon redundancy, so some limited damage in the payload region can be repaired during recovery. This is meant to help with a small amount of storage corruption or transmission damage.
Important limits:
In practice: minor corruption may be recoverable, but Timelocked is not a substitute for keeping backups.
Encryption keeps the content private until the unlock work is done. AEAD adds a tamper-evident seal: if the .timelocked file is corrupted or modified, Timelocked can detect that and fail loudly instead of producing wrong output.
AEAD (Authenticated Encryption with Associated Data) is required because it provides both:
K is recovered.K): detects tampering and corruption.This is important for Timelocked files because:
In short: the time-lock controls when K is obtained; AEAD ensures decrypted output is the exact original bytes once K is obtained.
No. AEAD can tell you that the file was decrypted with the right key and was not modified, but it cannot tell you who created it. Proving authorship requires a separate digital signature.